Differences Between Cloud Security and On-Premise Security
Sven Gusek / 17.05.2024
Table Content
Critical differences between Cloud Security and On-Premise Security
Environment and Control
Scalability and Flexibility
Cost Structure
Compliance and Regulatory Considerations
Threat Management and Response
Disaster Recovery and Business Continuity
Find the best fit for your business
Hybrid Approach
Conclusion
Explore differences between Cloud Security & On-Premise Security. Find the best fit for your business based on control, cost, scalability, & compliance.
In today’s digital landscape, businesses must choose between cloud security and on-premise security. These are two distinct approaches to safeguarding information and systems, each with unique characteristics and challenges.
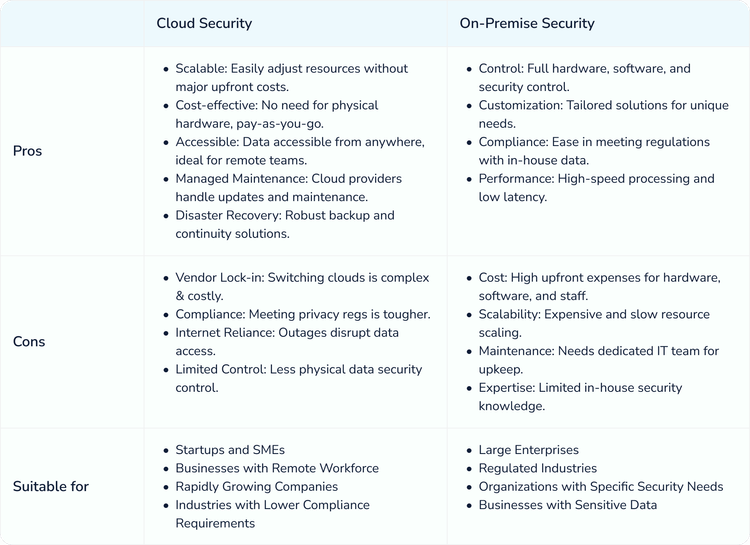
The critical differences between Cloud Security and On-Premise Security primarily revolve around the distinct environments, control models, scalability, cost structures, and compliance considerations associated with each. Here's a breakdown of these differences:
Critical differences between Cloud Security and On-Premise Security
Environment and Control
Cloud Security:
- Shared Responsibility Model: Security responsibilities are divided between the cloud service provider (CSP) and the customer. CSPs handle the security of the cloud infrastructure, including patching, vulnerability management, and baseline security measures, while customers are responsible for securing their data and applications within the cloud.
- Remote Management: Security measures are managed remotely, often with automated tools provided by the CSP.
- Abstracted Infrastructure: Users have limited control over the underlying hardware and must rely on the CSP for infrastructure security.
On-Premise Security:
- Full Control: Organizations have complete control over implementing and maintaining their security measures, from physical hardware to software configurations. This includes patching vulnerabilities, detecting threats, and responding to incidents. This requires a skilled IT security team.
- Localized Management: Security is managed on-site, allowing for direct oversight and customization.
- Tangible Infrastructure: Physical access to hardware allows for direct intervention and customization of security protocols.
Scalability and Flexibility
Cloud Security:
- Elasticity: Provides greater scalability, allowing you to easily scale storage and resources on demand. This is cost-effective for fluctuating needs, but you can have some control over specific security configurations.
- Global Reach: Security measures can be deployed globally with minimal latency, benefiting geographically distributed operations.
On-Premise Security:
- Fixed Capacity: Scalability is limited by the physical infrastructure, requiring significant investment to expand. Scaling up infrastructure can be expensive and time-consuming.
- Localized Reach: Primarily suited for localized operations, with additional complexity for securing remote locations.
Cost Structure
Cloud Security:
- OPEX Model: Costs are typically Operational Expenses, with pay-as-you-go models allowing for predictable budgeting. However, cloud service subscriptions can add up over time.
- Lower Initial Investment: Lower upfront costs as infrastructure is rented, not purchased.
On-Premise Security:
- CAPEX Model: Costs are primarily Capital Expenses, with significant initial investment required for hardware and software to manage the infrastructure.
- Maintenance Costs: Ongoing costs for maintenance, upgrades, and staffing.
Compliance and Regulatory Considerations
Cloud Security:
- Shared Compliance: CSPs often provide compliance certifications and help customers meet regulatory requirements, though customers must ensure their own compliance for data and applications.
- Third-Party Audits: Rely on CSPs for third-party audit certifications and compliance documentation.
On-Premise Security:
- Direct Compliance Responsibility: Organizations must directly manage and demonstrate compliance with all relevant regulations.
- Tailored Compliance: Easier to implement highly customized security measures to meet specific regulatory needs.
Threat Management and Response
Cloud Security:
- Advanced Threat Detection: CSPs often provide advanced threat detection and mitigation tools, leveraging large-scale data analysis and AI.
- Rapid Updates: Security patches and updates are often automatically managed by the CSP, ensuring timely protection against emerging threats.
On-Premise Security:
- Custom Threat Management: Organizations can deploy highly customized threat detection and response systems tailored to their specific environment.
- Manual Updates: Requires dedicated IT staff to manage security updates and patches, which can be slower than automated systems.
Disaster Recovery and Business Continuity
Cloud Security:
- Built-In Resilience: Cloud providers often offer built-in disaster recovery and business continuity solutions with geographically redundant data centres.
- Rapid Recovery: Ability to quickly spin up resources in different locations in the event of a disaster.
On-Premise Security:
- Customized Solutions: Organizations must design and implement their own disaster recovery and business continuity plans.
- Physical Dependency: Recovery may be slower and more complex due to dependency on physical infrastructure.
Find the best fit for your business
Hybrid Approach
Many businesses adopt a hybrid approach, combining both cloud and on-premise solutions to leverage the benefits of both. This can be particularly effective for:
Balancing Costs and Control: Using the cloud for general operations while keeping sensitive data on-premise.Gradual Transition: Allowing a step-by-step migration to the cloud while maintaining some critical systems in-house.Optimized Performance: Keeping latency-sensitive applications on-premise while using the cloud for scalable, less time-critical tasks.
Conclusion
The choice between cloud security and on-premise security depends on factors such as the level of control desired, scalability needs, budget constraints, regulatory requirements, and organizational resources. Cloud security offers flexibility, cost efficiency, and advanced tools, while on-premise security provides maximum control and customization.
Each approach has its advantages and challenges, and often, a hybrid approach that combines both may be the most effective strategy for many organizations. Consider your budget, IT expertise, and compliance requirements when making your decision.