Insider Threats vs. External Threats: A Drill Down
Sven Gusek / 09.05.2024
This blog post will delve into the critical distinction between insider and external threats, helping you understand the cybersecurity landscape.
Cybersecurity isn't just about building a fortress to keep hackers out. Not all threats come from the outside. Some of the most damaging attacks can originate from within the organization itself, by people who already have authorized access to your systems and data. These insider threats can be just as devastating as attacks from external threats like hackers and cybercriminals.
The Insider Threats: A Wolf in Sheep's Clothing
Insider threats pose a more insidious challenge. These threats come from individuals with authorized access to your systems and data, including employees, contractors, or even business partners. Unlike external threats, insiders already have a foot in the door, making their actions much harder to detect.
Imagine a disgruntled employee with access to customer data or a careless contractor who clicks on a suspicious link. Insider threats can be malicious, driven by revenge, competitors looking for strategic advantage, or individuals motivated by financial gain. But they can also be unintentional – a simple mistake can expose your entire network. For example, an employee falling victim to a phishing scam or downloading malware can unknowingly expose the entire organization.
The potential damage caused by insider threats can be significant. With their existing access, insiders can bypass security measures and:
- Steal sensitive data: Easily copy or transfer confidential information without raising suspicion.
- Sabotage systems: Cause significant disruption by deleting data or manipulating critical infrastructure.
- Sell access to external attackers: Open the door for external threats to exploit, leading to a larger-scale attack.
The biggest challenge with insider threats is their inherent trustworthiness. They already have legitimate access to systems and data, allowing them to bypass security measures designed to deter external attacks. Additionally, their knowledge of the organization's internal workings makes them particularly dangerous. They can target vulnerabilities with greater precision and fly under the radar by mimicking legitimate user activity.
The External Threats: The Classic Cybercriminals
External threats, on the other hand, are the more traditional cybersecurity foe. These threats come from attackers outside your organization. These are the more familiar cybercriminals we often think of – hackers, botnets, and state-sponsored actors. Their goals can range from stealing valuable data to disrupting operations (denial-of-service attacks) or conducting industrial espionage, including:
- Data theft: Stealing sensitive information such as financial records, customer data, or intellectual property.
- Disruption: Disabling or sabotaging critical systems to cause downtime and financial losses.
- Financial gain: Deploying ransomware or other extortion tactics to extract money from the organization.
Common tactics used by external threats include:
- Malware: Malicious software like viruses, worms, and ransomware that can infect devices, steal data, or disrupt operations.
- Phishing Attacks: Deceptive emails or messages designed to trick users into revealing sensitive information or clicking on malicious links.
- Hacking Attempts: Exploiting vulnerabilities in software, hardware, or network configurations to gain unauthorized access to systems and data.
- Social engineering: Exploiting human psychology to manipulate users into divulging sensitive information.
Spotting the Difference: Vigilance is Key
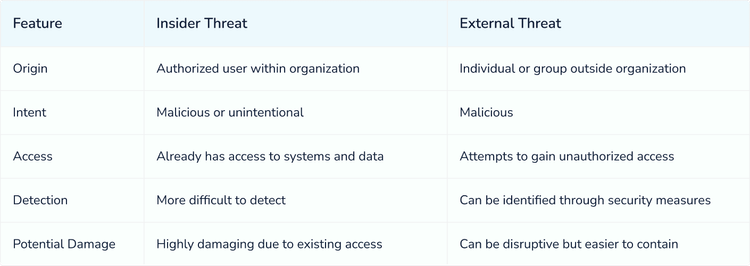
While both insider threats and external threats pose significant risks, they often leave different trails. External threats are typically easier to detect with security tools like firewalls that monitor network traffic for suspicious activity. However, insider threats can be much harder to identify due to their trusted access and ability to blend in. This is where user behaviour analytics (UBA) comes in. UBA monitors user activity for unusual patterns that might indicate an insider threat. Here's a quick breakdown of the key differences:
Building a Strong Defense: Security on Multiple Levels
Combating both insider threats and external threats requires a layered cybersecurity strategy that goes beyond just basic security software. Here are some key elements for a strong defense:
- Robust Security Controls: Implement firewalls, intrusion detection/prevention systems (IDS/IPS), data encryption, and access controls that limit access based on the principle of least privilege.
- Security Awareness Training: Regularly educate employees on security best practices, phishing scams, and how to identify and report suspicious activity. Foster a culture of cybersecurity awareness within your organization.
- User Activity Monitoring: Utilize UBA tools to detect anomalous user behaviour that might indicate an insider threat.
- Background Checks: Conduct thorough background checks on employees and contractors before granting access to critical systems and data.
- Incident Response Planning: Develop a well-defined incident response plan that outlines procedures for detecting, containing, eradicating, and recovering from security breaches, regardless of their source.
Conclusion
By understanding the unique characteristics of both insider and external threats, and implementing a proactive, multi-layered security approach, organizations can significantly reduce their cybersecurity risks and safeguard their valuable data and assets. Remember, cybersecurity is a team effort. With everyone in your organization playing their part, you can create a more secure digital environment for your business.